Recent Blog Entries
New Bloggers
User login
- Create new account
- Request new password
Navigation
Poll
Oracle and Google
Oracle and Google
I heard Marissa Mayer talk at BayChi. This is a Xerox-Parc hosted monthly lecture series about human computer interaction trends and happenings. Her most amusing anecdote at this particular lecture was about the first round of usability testing at Google. They put users in front of google.com, a purposefully sparse site. Most of them would not get started with the task (searching for X), even though they were prompted to do so. When asked about their hesitation they explained that they were "waiting for the rest of the page to load". Google staff then added a copyright footer to the page to communicate that it was OK to proceed...
It took a couple of mails to get a meeting with Marissa, or the person the press is calling "Google's secret weapon". I grabbed a cross-divisional crew of VPs and architects from Oracle and we talked about 5 possible collaboration areas between the two companies. As is normal in business development, only one of them "fired" as a follow up.
A connection was formed between Oracle and Dave Girouard, vice president and general manager of Google's enterprise business, as well as Matthew Glotzbach leading the effort on his team. Add a few months, a large number of developers and executives on the Oracle end, including one boardroom appearance, and we were off and running on a project to connect Google OneBox with Oracle's E-Business Suite.
When we define goals and user expectations for Oracle Fusion applications we do not normally think of SAP as a benchmark. A given user of HR or Financials will not be comparing us to our direct competitors. Their expectations for interactivity, quality, and even search behavior will come from companies like Google, Yahoo, and Microsoft. Oracle has long been a recognized innovator. We are now joining the ranks of innovators in the user experience area. If we want to meet user expectations we need to understand the models in the consumer space and map them to our unique business needs and our customers' desires. Charles Phillips, Oracle's President sent me this quote to emphasize the point: "Enterprise applications house valuable content that HR, Finance, and other professionals would like to search. It's not surprising that these enterprise users expect the same search functionality and ease of use that they've become accustomed to on the Web."
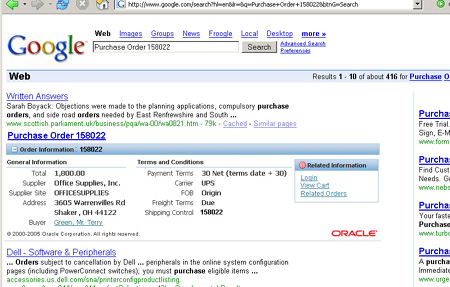
Here is an example of how this would work in the browser in our 11i version of applications. This is a screenshot of a user searching for a Purchase Order. An Oracle customer no longer needs to hunt and peck among multiple menu trees. They can find an object or function they are interested in by simply using language. More details can be found on Oracle's site, or on Google's site
The combination of Google and Oracle makes sense. Oracle's reputation in the area of enterprise applications, security, and open standards, together with Google's mindshare and innovative user experience will yield positive results for the end user.
Next installment will focus on the connection between user interface design and the rest of the design world: architecture, horology, automotive design, and other related disciplines
Trackback URL for this post:
On-Demand Security Audits and Vulnerability Management This white paper explains the value of the various approaches to network security. It focuses on the unique role of vulnerability management, and automated security audits in particular. The paper concludes with a description of the QualysGuard solution.
Buyers Guide for Online Backup + Recovery for SMBs Gartner Group projects that by 2008, the majority of data restores will occur from disk, not from tape. Establish your own evaluation checklist of capabilities to decide what matters most as you assess online backup and recovery solutions.
Ensuring Security and Compliance through Automated Patch Management Today's data centers are increasingly under attack. Hackers are able to compromise organizational security within minutes or days of a vulnerability announcement. In the face of today's security challenges, IT organizations are forced to respond quickly, decisively and efficiently in patching systems while minimizing any downtime impact.
About This Author
Name: Luke Kowalski
Company: Oracle
Job Title: Corporate UI architect
Bio: Luke Kowalski is the corporate UI architect at Oracle. His role serves to bridge the user interface (UI) design groups at Oracle, and he works as an evangelist for effective UI technology, on legal aspects of user interfaces, business context and partnerships, as well as cross-divisional information architecture integration. Before coming to Oracle, he worked for various startups as director of UI and Web, as well as for Netscape's Server and ECommerce divisions. He holds several UI patents, a CPE Certification, and serves as an ISO representative for US through ANSI. His educational background includes advanced degrees from UTA, Pratt Institute, and Columbia University.
Most Active Discussions
- Visa Seeks New Ways to Keep Data Secret(0)
created: 08/29/2005 - Adam Bosworth on Service Architecture(0)
created: 04/01/2003 - On Display(0)
created: 11/28/2005 - Alliance Modeling(0)
created: 10/27/2005 - Service is Marketing(0)
created: 09/14/2005
Syndicate
Popular Topics
Sponsored Links
Browse archives
| Su | Mo | Tu | We | Th | Fr | Sa |
|---|---|---|---|---|---|---|
| 1 | ||||||
| 2 | 3 | 4 | 5 | 6 | 7 | 8 |
| 9 | 10 | 11 | 12 | 13 | 14 | 15 |
| 16 | 17 | 18 | 19 | 20 | 21 | 22 |
| 23 | 24 | 25 | 26 | 27 | 28 | 29 |
| 30 |